Your internet-exposed systems are getting hit by opportunistic attacks within hours of vulnerability disclosure.
Last year, ToolShell meant attackers could run code on internet-facing SharePoint servers without needing credentials – and because SharePoint is Active Directory connected, they were starting in a highly sensitive part of the environment.
When it went public, Intruder’s research found thousands of exposed SharePoint instances. Most of them had no reason to be public-facing.
So why does this happen?
Intruder’s Head of Security walks through why critical exposures get missed.
✅ Read the blog to learn more: https://lnkd.in/egTs9f_G
Transcript
Transcript
Transcript
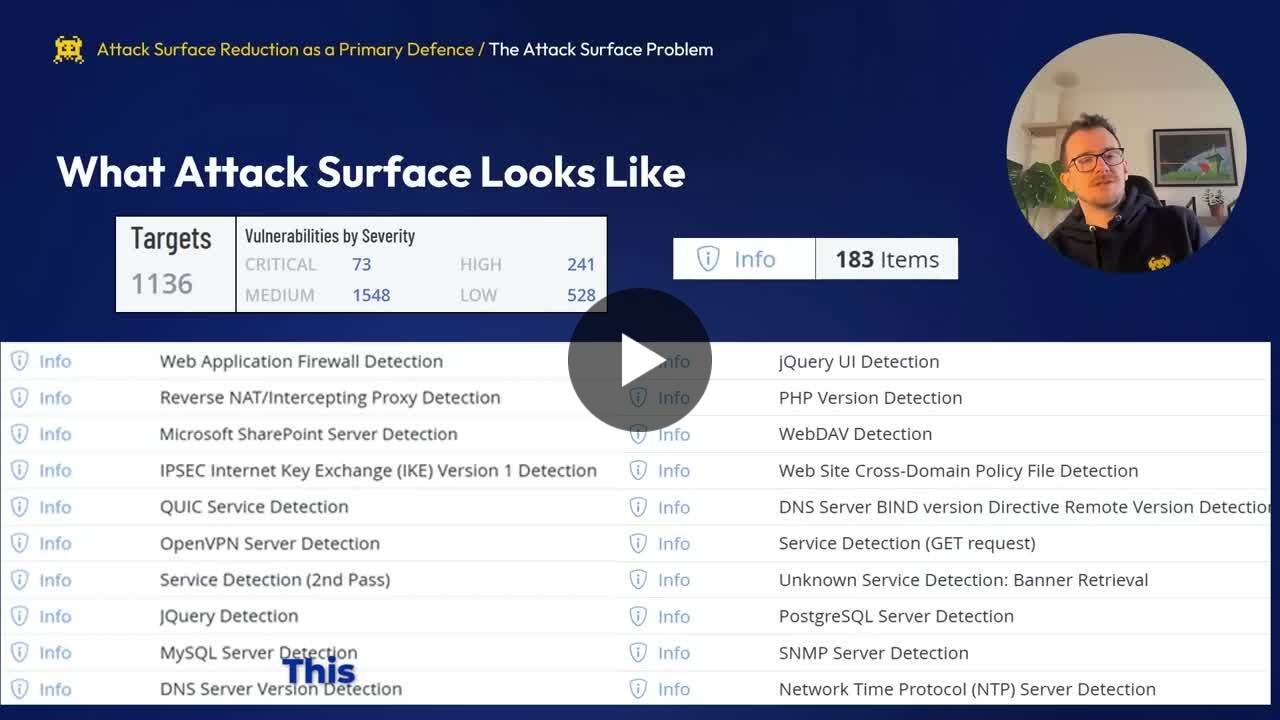
This is what attack surface can look like in your vulnerability scanner. We have some scan results here for 1000 targets. You can see it found lots of different vulnerabilities and criticals and highs and mediums and lows. But for the purpose of this argument, we’re going to look at the informationals. So in this particular scam, there were 183 informational items, just quite a lot to look through. At first glance, they don’t look that interesting. So if you take the top one there, web application firewall detection, This scam ran from the Internet. It ran from a perimeter. Perspective so you would expect to see a web application firewall there but when we dig a little bit further into these informationals we find that some of them perhaps shouldn’t be an informational at all so the the obvious one there is Microsoft SharePoint Server detection. This could be why some of those organizations some of those thousands with SharePoint on the Internet have it on the Internet because it’s hidden in their informational scan results and perhaps they never review their informational database should only be exposed to the application and not generally exposed to the Internet because. The same reason if a zero day gets fined found in Postgres, then those opportunistic attackers are going to have a much easier time exploiting your systems, and you’re gonna have much less time to hatch. What?