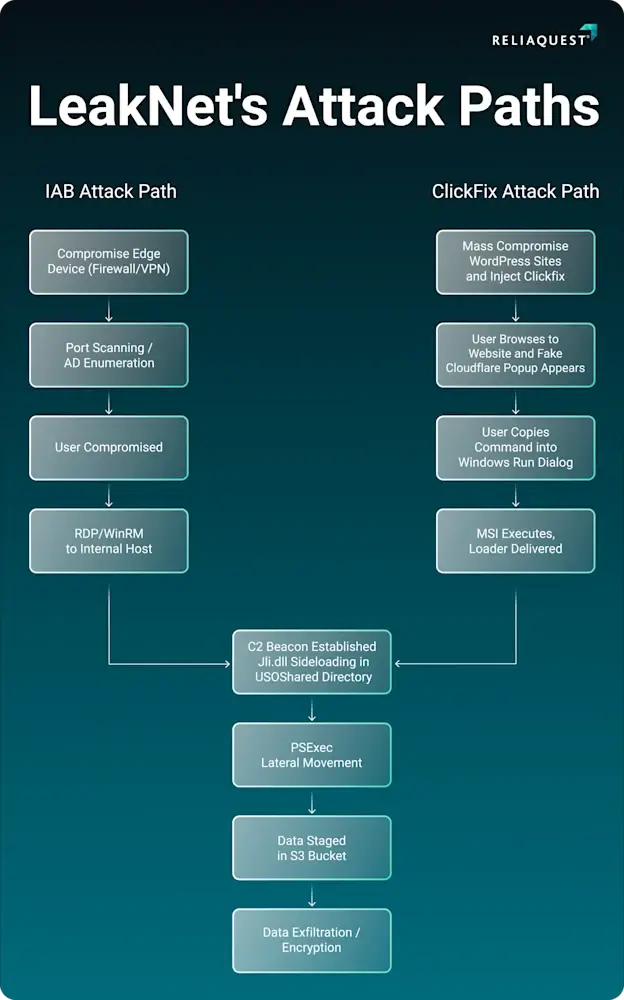
The ransomware group known as LeakNet is rapidly upgrading its attack methods to infect more victims. Previously averaging three targets per month, the group is now moving away from buying stolen network access from other hackers.
Instead, LeakNet is launching its own campaigns using fake error screens and a stealthy new tool that runs malicious code directly in a computer’s memory.
Despite these new entry methods, the hackers always use the same predictable steps once they get inside a network, giving defenders a clear chance to stop them before files are encrypted.
LeakNet Adopts ClickFix and Deno Loader
The first major change in LeakNet’s strategy is the use of ClickFix lures. This is a social engineering trick where hackers compromise a legitimate website and display a fake security check, such as a bogus Cloudflare Turnstile page.
The page tricks the visiting user into copying and pasting a malicious command into their computer’s run dialog.
This approach allows LeakNet to cast a wide net and target anyone browsing the web, greatly reducing their cost per victim. By generating their own entry points, the attackers bypass the need to wait for valuable accounts to appear on dark web markets.
This “bring your own runtime” technique leaves almost no evidence on the hard drive, making it extremely difficult for traditional antivirus software to detect.
The Deno loader gathers information about the infected machine, contacts the attacker’s server, and continuously fetches more malicious code without saving normal files. Because Deno is a trusted tool, standard security blocklists often ignore its activity.
A Predictable Post-Exploitation Playbook
| IOC Type | Details |
|---|---|
| ClickFix Domain | tools.usersway[.]net, apiclofront[.]com, sendtokenscf[.]com, binclloudapp[.]com |
| Deno C2 Domain | okobojirent[.]com, mshealthmetrics[.]com, verify-safeguard[.]top, cnoocim[.]com, delhedghogeggs[.]com, serialmenot[.]com, crahdhduf[.]com |
| Deno C2 IP Address | 194.31.223[.]42, 144.31.2[.]161, 87.121.79[.]6, 87.121.79[.]25, 144.31.54[.]243, 144.31.224[.]98 |
| Sideloaded jli.dll C2 Domain | neremedysoft[.]com, ndibstersoft[.]com, windowallclean[.]com |
| Malicious S3 Bucket | fastdlvrss.s3.us-east-1.amazonaws[.]com, backupdailyawss.s3.us-east-1.amazonaws[.]com |
Following this step, the attackers check the system for active user credentials using a built-in Windows command. Armed with these credentials, they move sideways through the network using PsExec, a standard administrative tool.
Finally, LeakNet uses standard Amazon S3 buckets to stage its payloads and steal sensitive data. Because they abuse standard administrative tools and cloud services, their behavior blends seamlessly into everyday network traffic.
To protect against these threats, defenders should focus on monitoring suspicious behavior rather than just looking for known bad files.
Reliaquest security teams must watch for unusual commands initiated by web browsers, unexpected connections to cloud storage from standard endpoints, and tools like Deno running outside of normal developer environments.
By isolating machines as soon as predictable patterns appear, organizations can disrupt the attack before ransomware is deployed.
Follow us on Google News , LinkedIn and X to Get More Instant Updates. Set Cyberpress as a Preferred Source in Google.

