727 Attacks in December Targeted Healthcare, Manufacturing as Cybercriminals Exploited Holiday Staffing Gaps
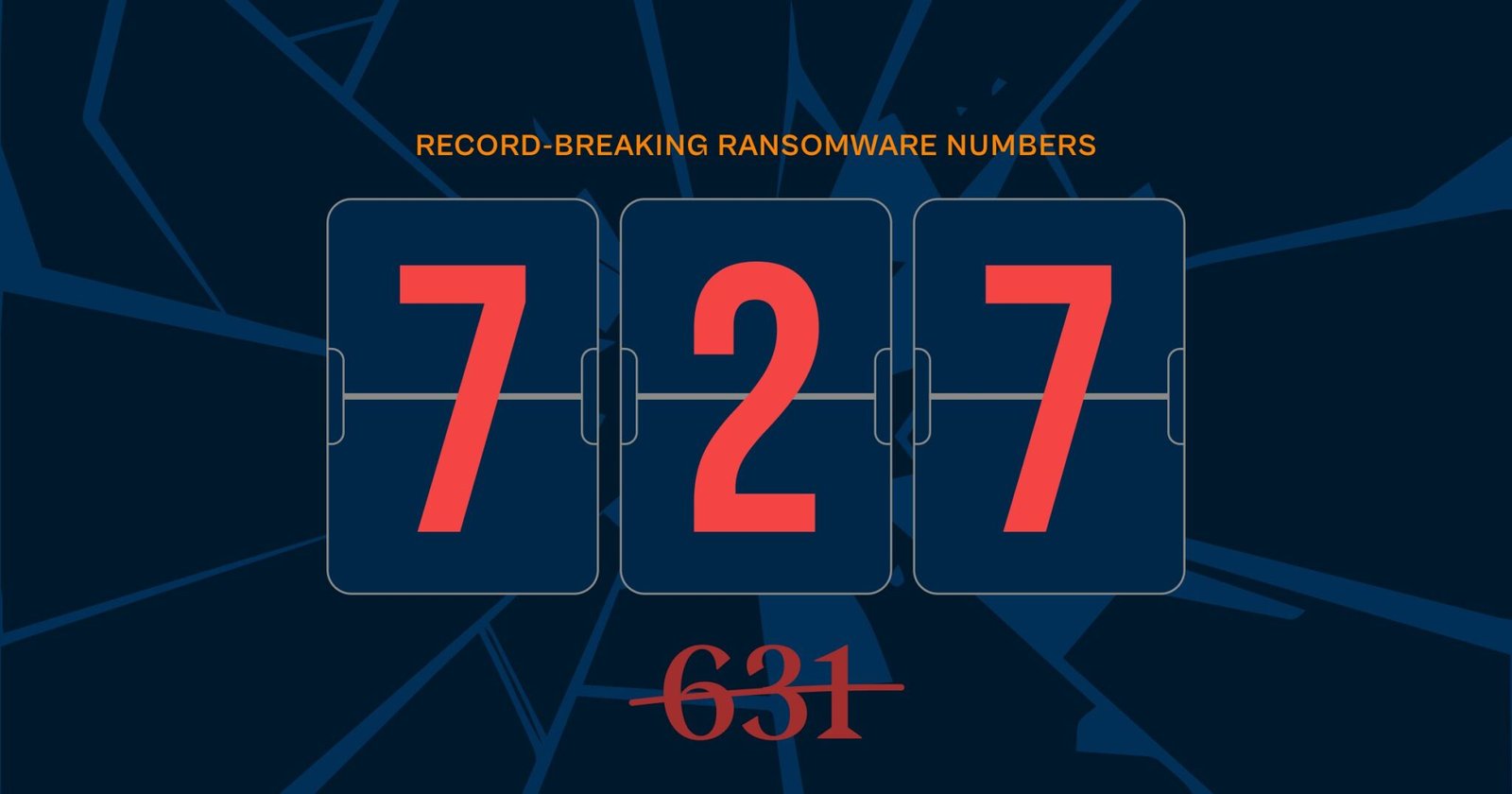
December 2025 broke every record. With 727 confirmed attack claims, the month surpassed October’s previous high of 631 by 15.2%. The expected holiday slowdown never arrived. Qilin led with 162 claims, but LockBit’s sudden return after 10 months of near-silence stole the month: 96 attacks, representing 83% of their entire 2025 total, all compressed into four weeks.
Four emerging ransomware operations conducted notable campaigns throughout December: Kazu, Benzona, TridentLocker, and MintEye. Collectively they claimed over 30 victims across government agencies, healthcare providers, and critical infrastructure worldwide.
Manufacturing and construction bore the heaviest burden. Healthcare took 45 attacks, continuing a pattern that has persisted throughout 2025. North America absorbed 53% of all attacks, with the United States alone at 47.6%. The four featured emerging actors recorded 12 attacks across 7 industries and 6 countries in their first months of operation.
On the ground, holiday-period attacks disrupted food production, education, and municipal services. Recovery timelines stretched from days to indefinite. Organizations faced encrypted systems and, simultaneously, their stolen data appearing on leak sites. Disclosed ransom demands stayed in the $60,000 to $80,000 range for publicly reported cases.
HAL (Halcyon Attack Lookout)
Data period: December 1-31, 2025 (Complete) | RECORD MONTH
Top Threat Actors
Threat Actor Feature of the Month
Top Targeted Industries
Regional Distribution
Top Countries
Featured Emerging Actors: December Activity
Halcyon Ransomware Research Center
Qilin: December 2025 Threat Actor Feature
Sinobi: Threat Actor Profile (December 2025)
Nightspire: Threat Actor Profile (2025)
LockBit’s December Resurgence
This is not simply a continuation of the LockBit brand. What emerged in December represents the fifth iteration of the operation (LockBit 5.0), following the disruption of LockBit 4.0 during Operation Cronos in February 2024. LockBitSupp, the group’s administrator, announced the 5.0 version in September 2025, promising improved infrastructure and new affiliate recruitment.
December activity followed a distinct pattern: 29 attacks in Week 1 (Dec 1-7), minimal activity in Week 2, renewed operations with 9 attacks in Week 3, then 48 attacks in Week 4 (Dec 22-31). That final week was the highest single week for any threat actor during the holiday period. Targeted organizations spanned 20+ countries across all continents, with particular concentration in manufacturing and professional services sectors.
The timing of the Week 4 surge coincided with reduced holiday staffing at many organizations, a pattern consistent with opportunistic targeting. Several security researchers have noted that the new leak site infrastructure differs from previous versions, and the affiliate network appears to include both returning operators and new recruits. Whether this resurgence represents sustained operational recovery or a temporary spike remains to be seen in early 2026.